Cybersecurity Awareness Month 2025 - Top 5 Phishing Attempts
As we approach the end of Cybersecurity Awareness Month as well as the latter quarter of 2025, we thought it may be of interest to highlight some of the most notable phishing emails that NEOMED staff, faculty or students received throughout the year. The list is in no particular order, and contains some of the most clever, conniving and perhaps humorous phishing emails we received this year.
Although intended to highlight some of the most notable cases for these reasons, it's also important to pay attention to the look and feel of these attempts, as they are real and recent, which you may happen to see in your inbox at one point or another. For the attempts with pictures available, we have removed the recipient addresses to ensure privacy.
Let’s look at the top five phishing attempts of 2025.
1. Varying Hotmail Addresses
To begin with one of the more unique and clever cases, throughout the spring and early summer of this year, several people at NEOMED reported receiving unsolicited messages regarding student loan debts and forgiveness from strange email senders, all using the Hotmail email service. Each sender used a different name and address, with various names such as “Arie Grundland” from completely randomized addresses like lrucgpagj7703[at]Hotmail[dot]com. This was a clever tactic, since every name, subject and sender address was different, it became more difficult to track down and block these messages. Fortunately, despite this being a clever tactic, the strange names and phrasing of each message made most recipients feel suspicious about them, and therefore they were reported or ignored by most. Additionally, the content of the email and patterns of the email addresses made it possible to implement some phishing rules to prevent reoccurrence.
2. New Submission from Contact Us
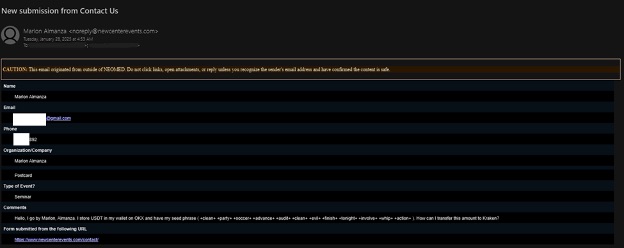
This one is from January 2025 and was leveraging the NEW Center Contact Us form. The sender claims the organization/company is their name/postcard, and the individual leaves a comment noting that they store USDT, a cryptocurrency, in their crypto wallet on OKX, and is wondering how they can transfer this to Kraken, a popular cryptocurrency exchange website. It is quite a strange phishing attempt – these are typically social engineering attempts made to entice people to return their inquiry and into trying to take the crypto currency for themselves, which is somewhat of a less commonly seen method, at least here at NEOMED.
3. “Your OneDrive are about to be deleted”
In this case, many users across NEOMED received an email, claiming that unfortunately, “Your OneDrive are about to be deleted.” Given the blatant grammatical mistake right off the bat, in addition to many more throughout the email, not to mention the unsolicited email asking for a hefty sum of 100 dollars to reactivate their account, it was obvious to those who received it that it was a phishing email. From here, it was quickly reported to the NEOMED IT Security team for review and assessment. Although attempts like this may seem laughable or clearly fake, it is still very helpful for these messages to be reported or forwarded to NEOMED IT so that we can prevent continued distribution and take appropriate action.
4. Disney+ Phillipines
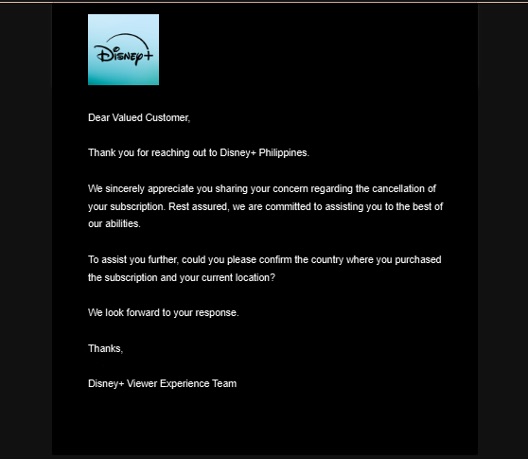
Another strange one, this time from Disney+ Phillipines. It was attached as a reply to a fake original message which made it appear that the recipient had asked Disney+ to cancel their subscription. This message then asks for the user to reply back with the county they supposedly purchased their subscription from, as well as their current location. Fortunately, the user reported the email as phishing pretty quickly and we were able to address it.
5. John Smith shared a OneDrive file/Google Doc with you
As our fifth and final mention, a currently popular phishing and credential harvesting method is that of the shared OneDrive or Google drive item. In this method, a bad actor posing as a colleague, student or point of contact, begins by sending an email sharing either a OneDrive file or Google Drive file, such as a document, slideshow or Excel sheet. Many of these emails look quite convincing and can come from legitimate email services, so the unwitting recipient clicks on the link to access the shared file. At this point, they are prompted to sign in to their NEOMED account to access said file, and often times the page will even ask the user to verify with an authentication method such as their authenticator app. Now the bad actor has intercepted the user’s login credentials and sometimes even a digital token from the victims' authenticator app and can gain access to their account – even with MFA in place. The important step in preventing these phishing attempts is not clicking on random links, especially those associated with an unprompted or random document sharing request you may receive.
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _
These are only a handful of many phishing attempts we received within the last year, and as such, these examples are not a perfect all-encompassing list of what you might expect to see in your own inbox. As such, it is important to remain vigilant, and to keep in mind that it’s always better to be safe than sorry. If you suspect an email is suspicious, please report it to NEOMED IT by using the Report Message button built into Outlook; you can also forward the message to IT Security, submit a Help Desk ticket, or give the Help Desk a call. Your cooperation and participation in reporting and documenting these threats is greatly appreciated and is vital to ensuring we maintain a secure cyber environment here at NEOMED.
- submitted by Dan Foster, IT